In Windows Azure Pack – Manage VM Networks topic, I have talked about network virtualization implemented with NVGRE and I have implemented it without NVGRE gateway. That means that Virtual Machines weren’t able to be contacted from the outside of its VM network boundary. In this topic, I’m going to implement a NVGRE gateway in order to these VM can be accessed from the physical world.
I will explain you how to implement a NVGRE Gateway based on the Windows Server Gateway. It is a Virtual Machine (or several for high availability) with Windows Server 2012 R2 and the RRaS server role. I will talk only about the using of NVGRE gateway with Network Address Translation (NAT).
Virtual Machine Manager is very important when using network virtualization because it is this last that configure the RRaS role and it is VMM that has the knowledge about the VM network configuration. So in a production environment you should implement VMM in high availability.
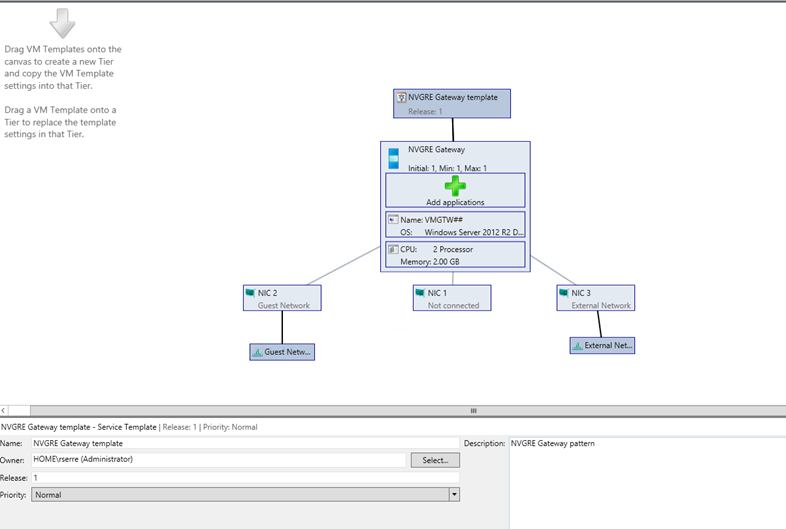
The below schema presents you the NVGRE gateway:

From the point of view of NVGRE gateway, two networks are needed:
- The Front-End network (Public IP addresses);
- The Back-End Network connected to the provider address (PA) network.
When a virtual Network is created, an external IP address from the Front-End network will be associated to this virtual network. If the Virtual Machine has to be contacted from the outside of the virtual network across NAT rules, the external IP address will be used.
Usually you need also an additional network for the management (Active Directory, DNS and so on).
Requirements
- To follow this topic you should have a working network virtualization (cf. this topic);
- A dedicated Hyper-V to host Windows Server Gateway VM ;
- A Front-End network with multiple Public IP addresses (in my example I will use private addresses because I can’t have several Public IP addresses);
- A VHDX with a Windows Server 2012R2 syspreped from a Gen1 VM (cf. this topic).
Network presentation
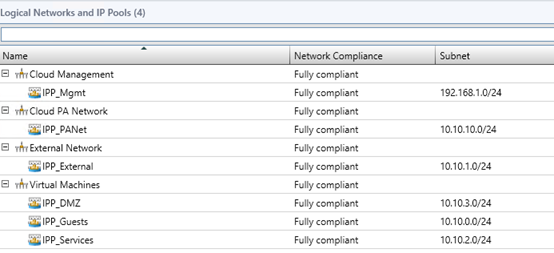
I have 4 different logical networks:
- Cloud Management: this is my network used for management;
- Cloud PA Network: this is the network for network virtualization;
- External Network: this is my Front-End network;
- Virtual Machines: this is VLAN-based networks for my infrastructure (Windows Azure Pack, System Center, Active Directory and so on).
Hyper-V host configuration
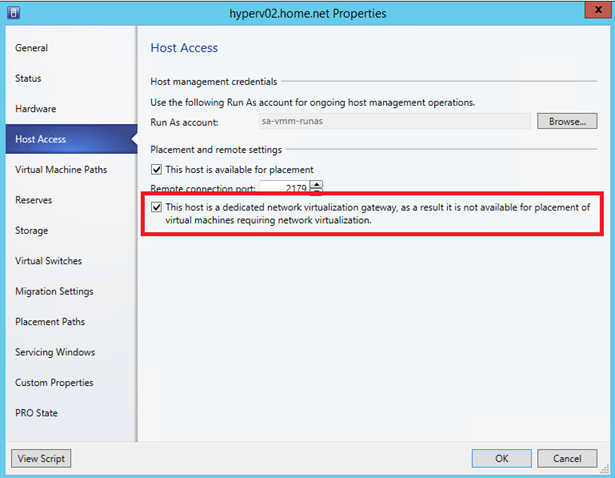
First you have to configure a Hyper-V host (or several for high availability) to dedicate it to the network virtualization gateway. For that right click on your Hyper-V host and click Properties. Select the Host Access tab
and tick the box as below. When this setting is activated, Virtual Machines in the network virtualization can’t be placed on this host.
Implement the NVGRE Gateway server
Service Template creation
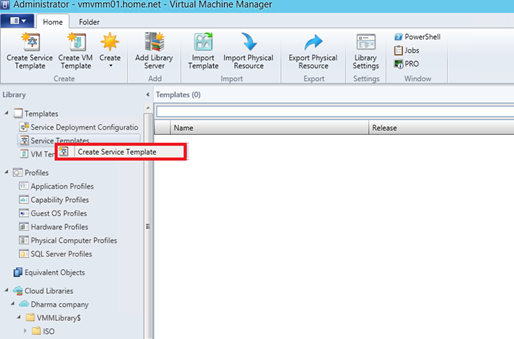
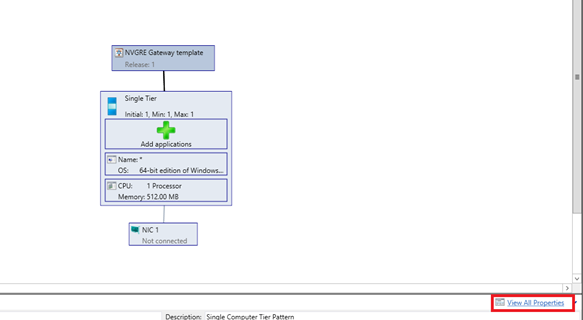
First we have to create a service template to deploy the gateway tier. So open the library tab and right click on Service Templates. Select Create Service Template.
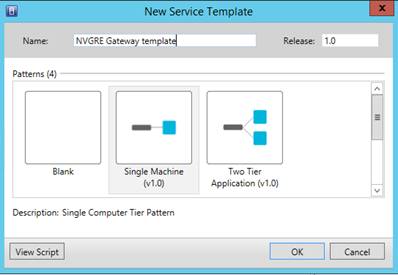
Give a name to your template and select Single Machine (v1.0).
Select the Single Tier and click on View All Properties.
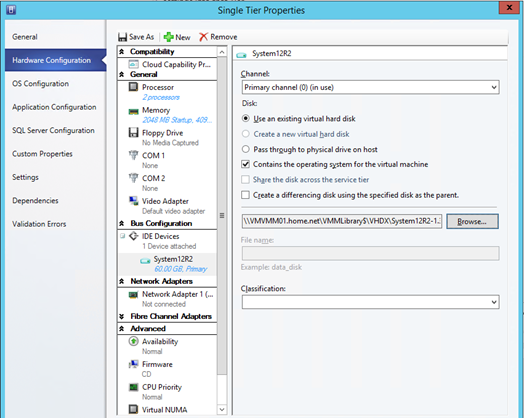
First, add an IDE hard drive. Specify the path to your VHDX with Windows Server 2012R2 syspreped.
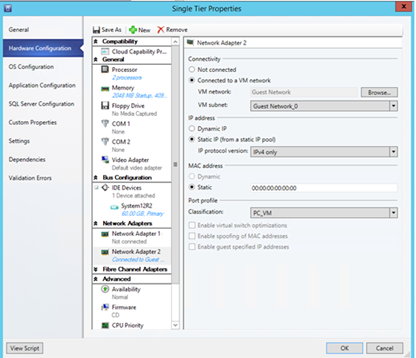
Remove the first network legacy adapter and create a new network adapter (not a legacy). Add a second network adapter and connect it to your management network. This network is used to communicate with the Active Directory, DNS and so on.
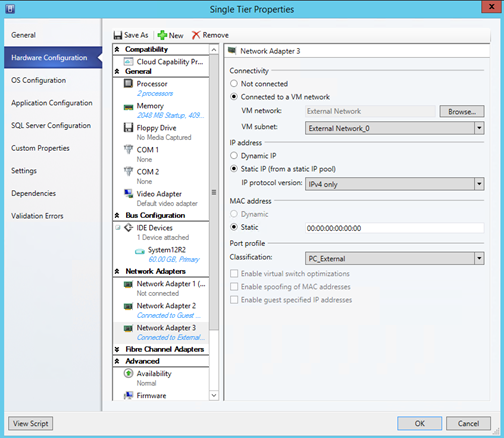
Add a third network card and connect it to your Front-End network.
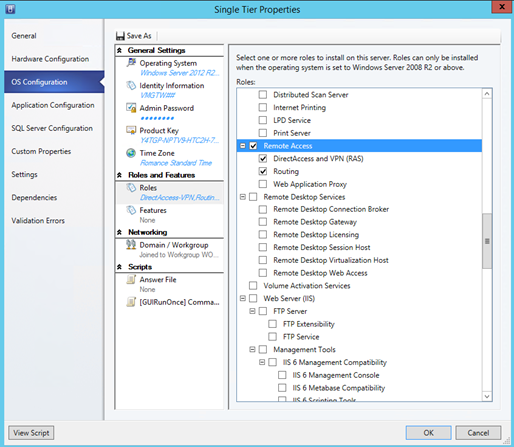
On OS Configuration tab, set the VM name, the product key (use an AVMA key) and add DirectAccess and VPN (RAS) and Routing service roles as below.
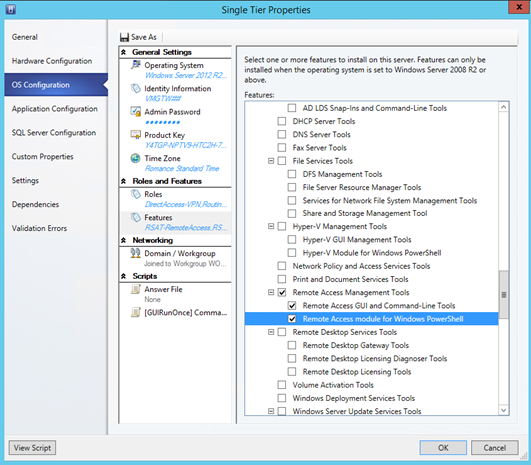
Add also RSAT for Remote Access role.
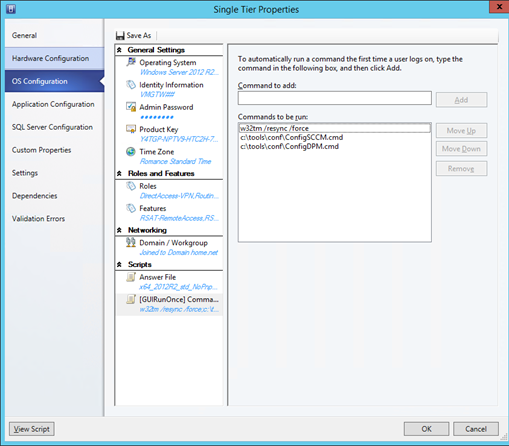
If you have some custom scripts to run at the first logon, you can add it in [GUIRunOnce] Commands:
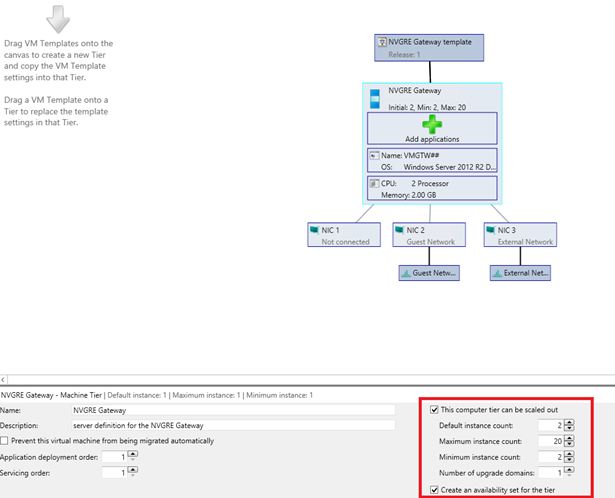
After you have finished setting properties, you should have something like below screenshot:
Configure service template for HA
If you need NVGRE Gateways in high availability, you have to enable This Computer tier can be scaled out and Create an availability set for the tier.
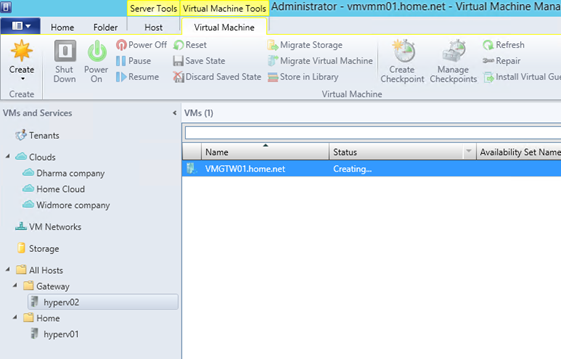
Deploy NVGRE Gateway Virtual Machine
Once the service template is ready, right click on it and select Configure Deployment.
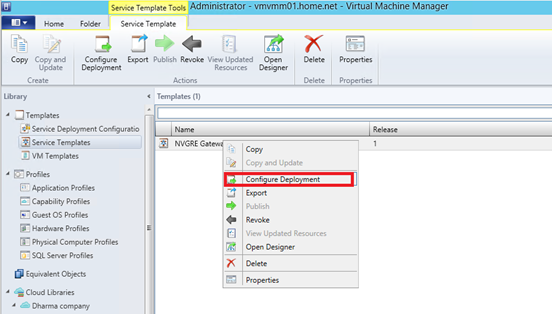
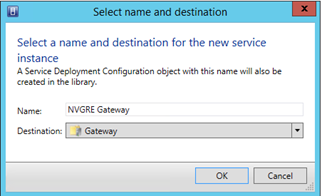
Select your Gateway host group and give a name to your service instance.
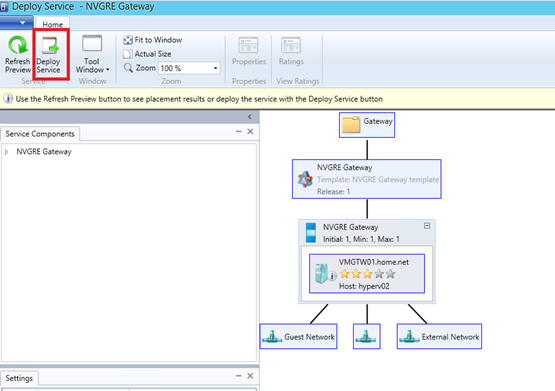
Just click on deploy service to start the NVGRE gateway VM creation.
Once the VM is created, open the properties of this last. Select the network adapter that is not connected. Now select Connected to a VM Network. Click on Browse and clear selection. You should have something as below screenshot:
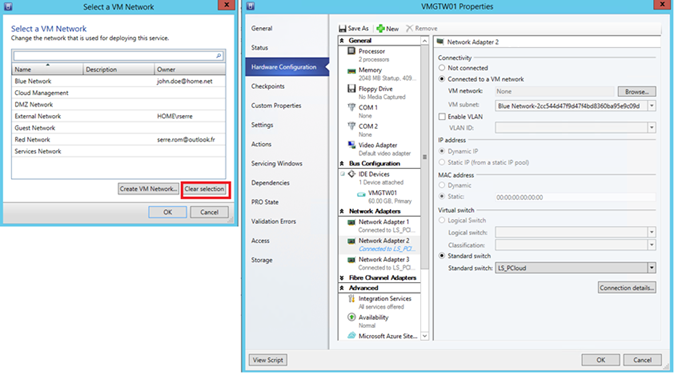
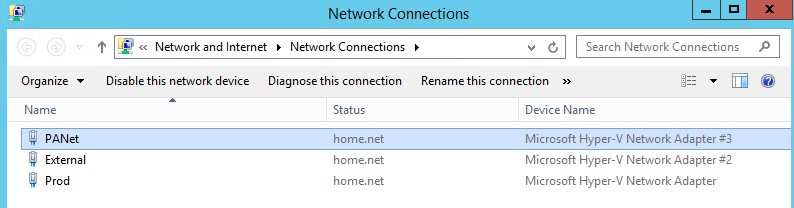
To finish start the server. I recommend you to rename network adapter inside the VM to simplify the configuration of the network service in VMM.
Add the network service
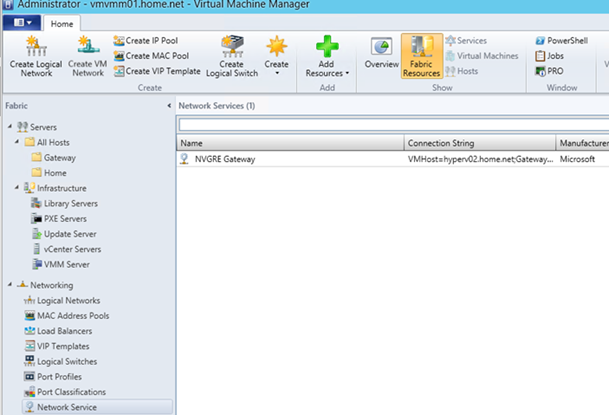
Now that the NVGRE Gateway server is ready, we have to add the network service to VMM. Navigate to the Fabric and right click on Network Service. Then select Add Network Service.

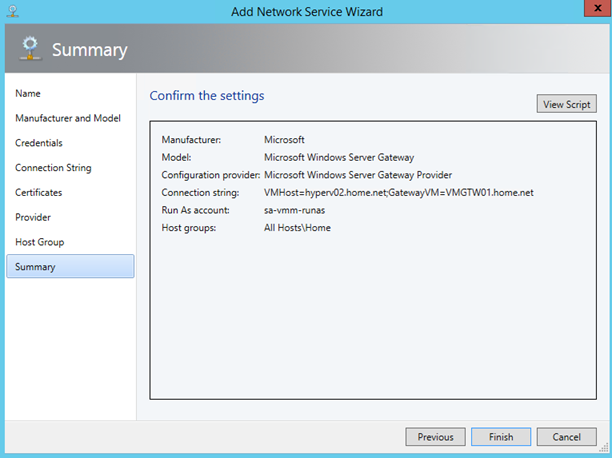
Give a name to your network service. I have called mine NVGRE Gateway.
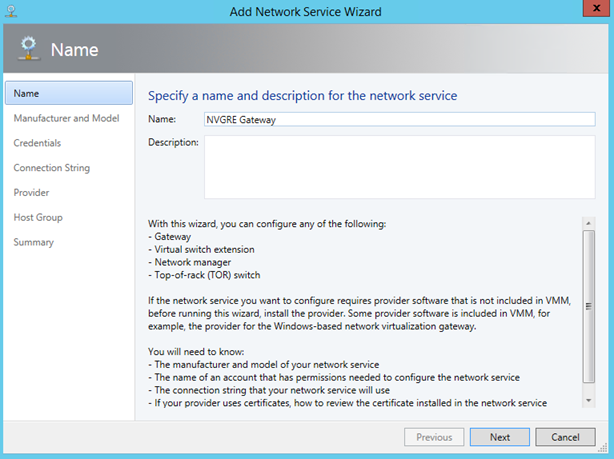
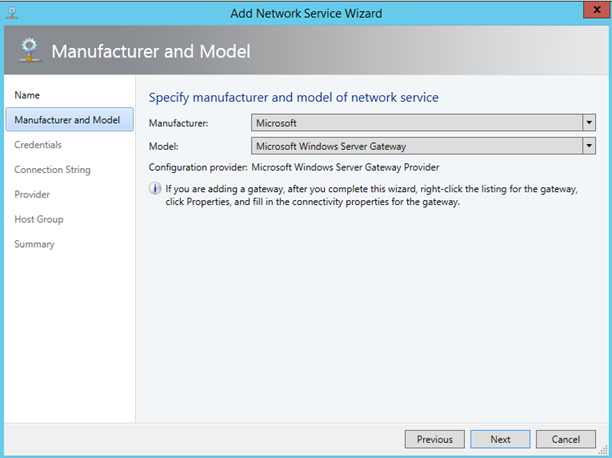
Next select Microsoft as Manufacturer and Microsoft Windows Server Gateway as Model.
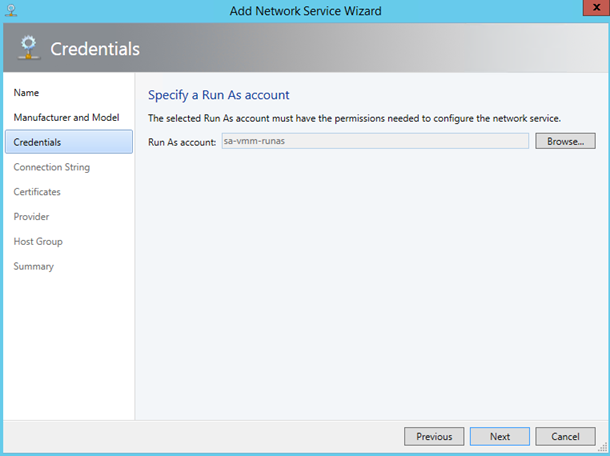
Then select a Run As account. This account should have administrative right on NVGRE gateway servers.
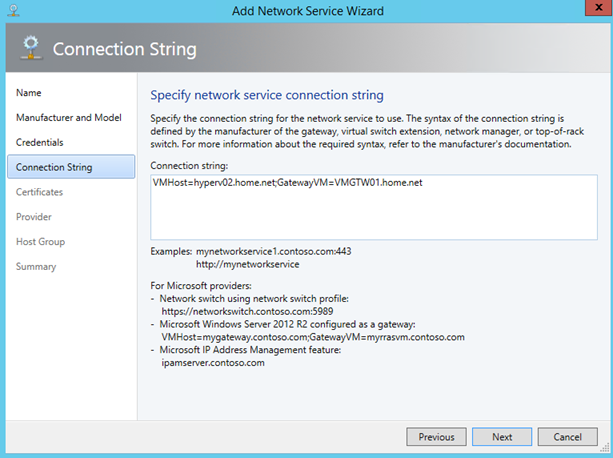
Next you have to specify the connection string:
- VMHOST: specify the FQDN of your Hyper-V (or the cluster in case of HA) which hosts your NVGRE Gateway;
- GatewayVM: specify the FQDN of the NVGRE gateway (or the cluster in case of HA).
So on my side the Connection string is as below.
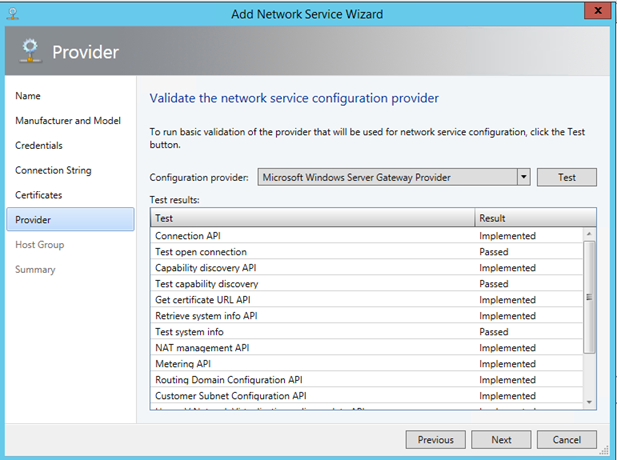
Click on Test to verify if all is ok on your NVGRE Gateway server.
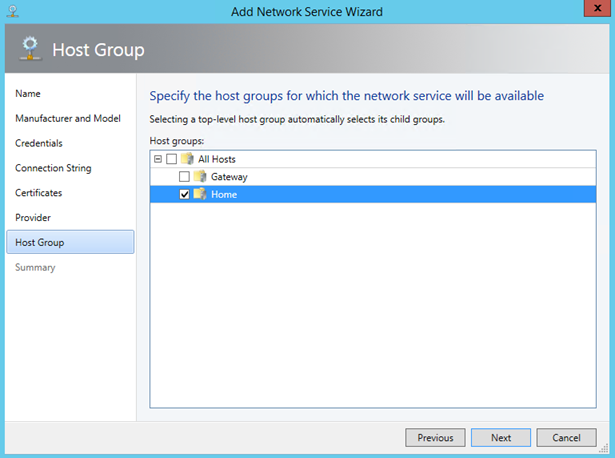
Select the host group where NVGRE Gateway will be available.
Click on finish and the network service should be added.
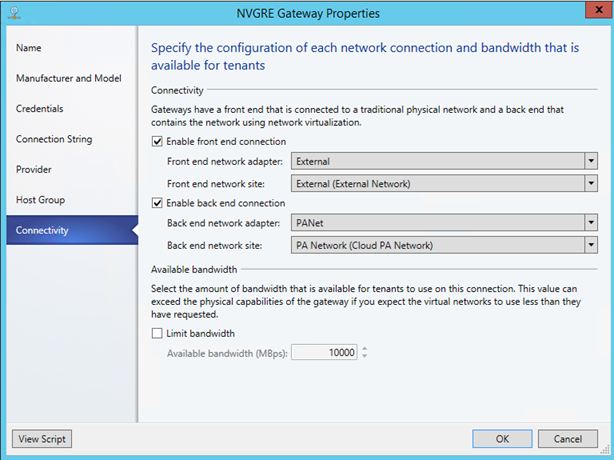
Now that the network service is created, right click on it and select properties.
On connectivity tab, associate the Front-End network adapter of the VM with the network site defined in VMM. Make the same thing for the back-end connection.
Use the NVGRE Gateway from WAP
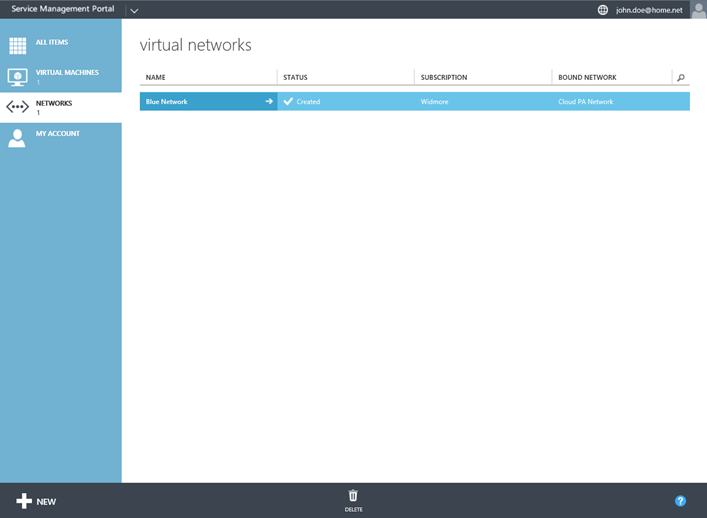
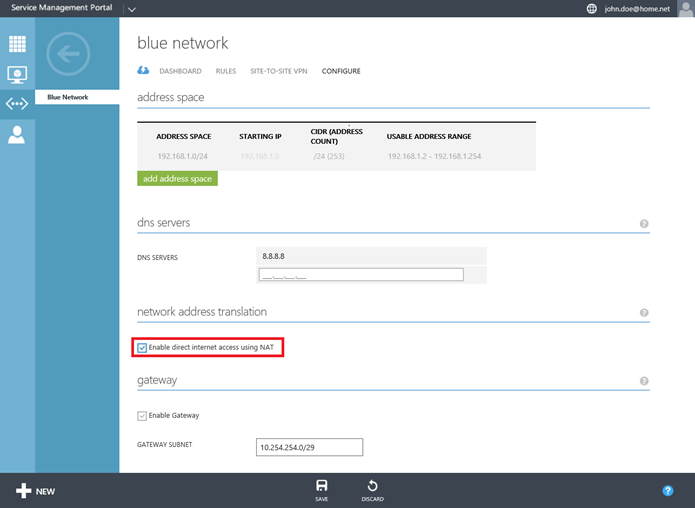
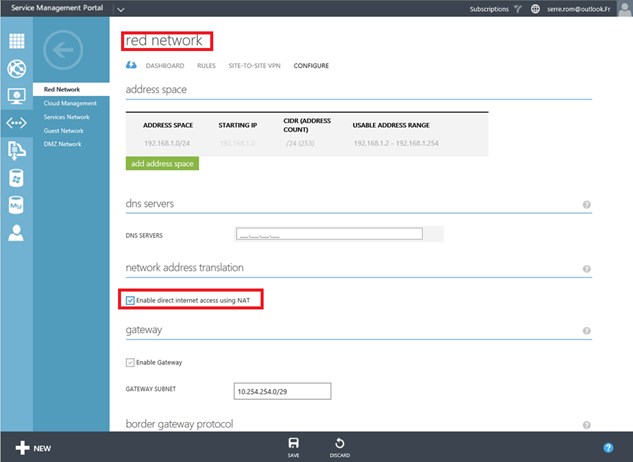
Open your tenant portal and open networks tab. Open the properties of one of your virtual networks.
Navigate to configure tab. Activate Enable direct internet access using NAT check box.
On dashboard tab, you should now have an External IP Address.
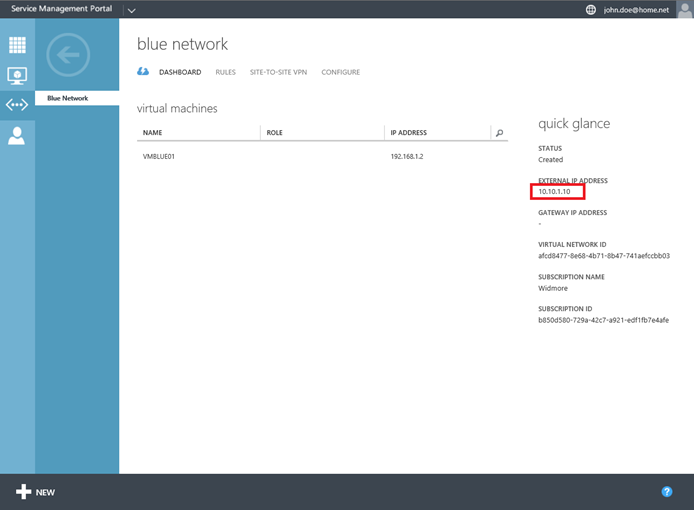
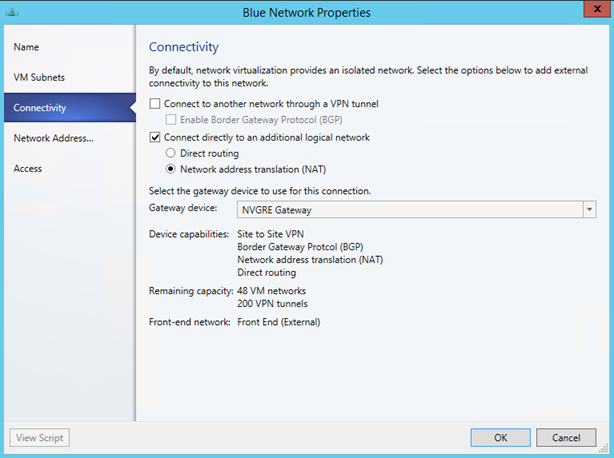
If you go back to VMM and open the properties of the Blue Network, the parameters in connectivity tab have been set as below:
If you run an ipconfig on the NVGRE Gateway server, an IP has been added on the external NIC:
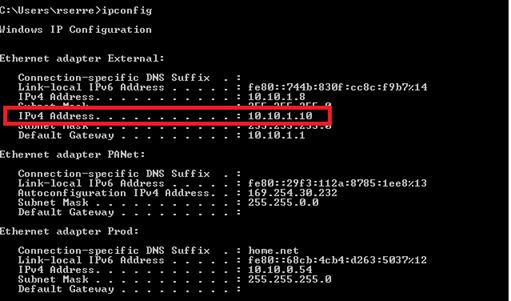
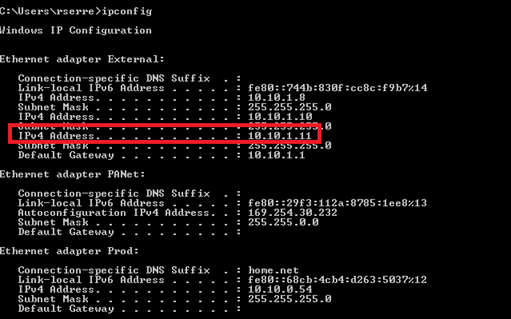
If I activate NAT on another virtual network, a new IP address should be added on the External NIC. Let’s try:
I run again ipconfig on the NVGRE gateway server:
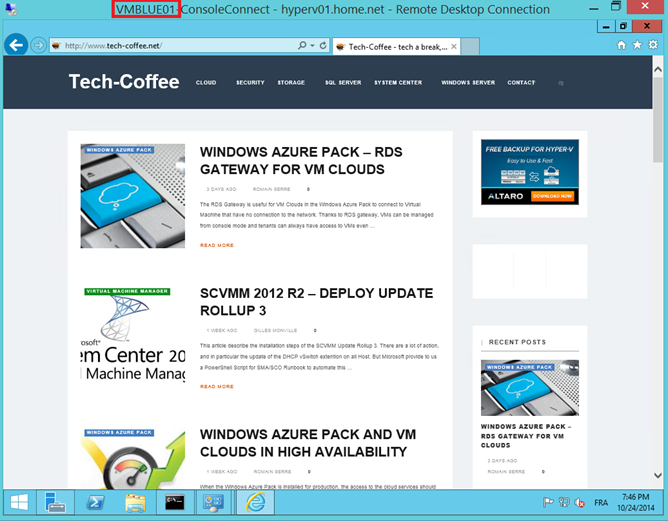
That’s work J. Now I’m connecting to VMBlue that is connected to the Blue virtual network to verify the Internet access:
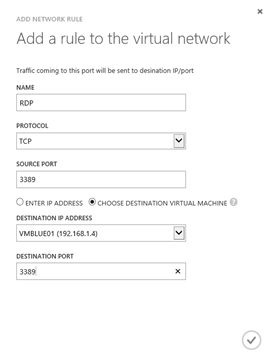
Add NAT rules from WAP
To add NAT rules, select rules tab on your virtual network and click on Add Rule.
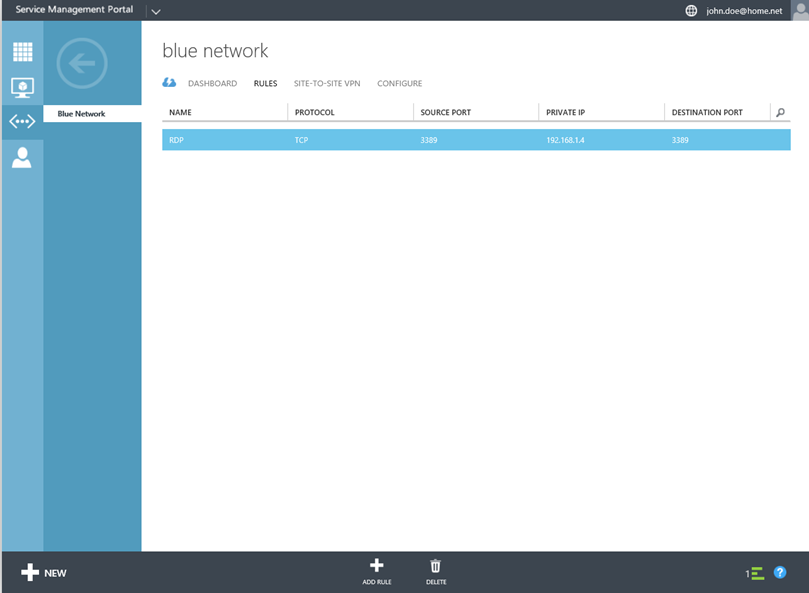
Specify settings and click on ok.
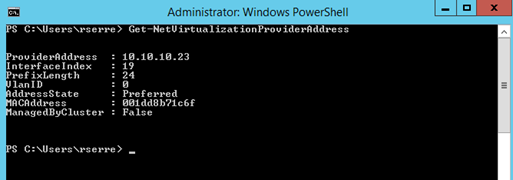
Commands for network virtualization
The first useful commandlet is Get-NetVirtualizationProviderAddress which has to be run in a Hyper-V host. It enables to obtain the IP address on the provider network:
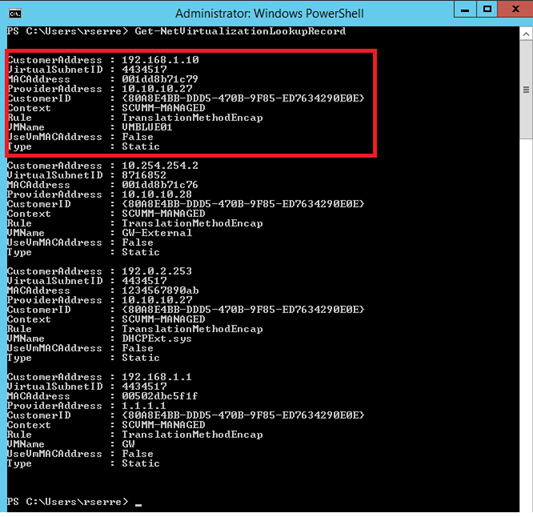
Thanks to the commandlet Get-NetVirtualizationLookupRecord, we can have network information about tenant’s virtual machines (VSID, customer address etc.):
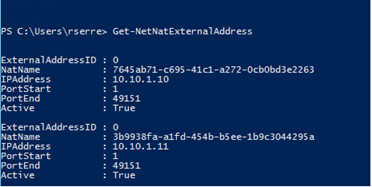
On the NVGRE Gateway server, you have access to Get-NetNat* commandlets. For example Get-NetNatExternalAddress shows us each external address configured. In the below capture there is one for Red network and one for Blue network.
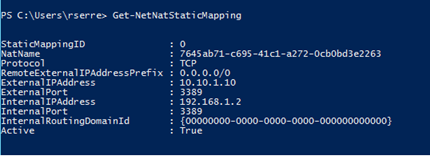
The Get-NetNatStaticMapping provides NAT rules information. Above I have configured a NAT rule for RDP. You can view this configuration with this commandlet:
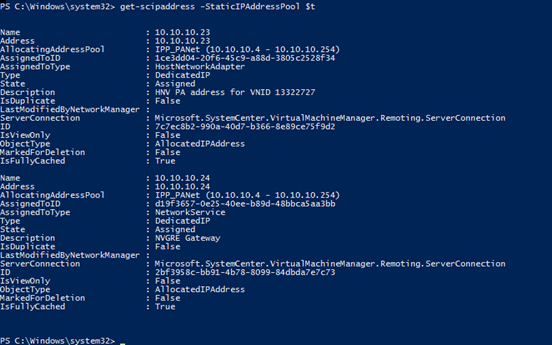
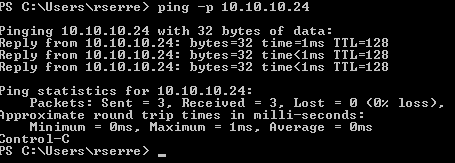
To finish let’s see the ping command on the Provider New. First I run Get-SCIPaddress to know which IP addresses have been allocated:
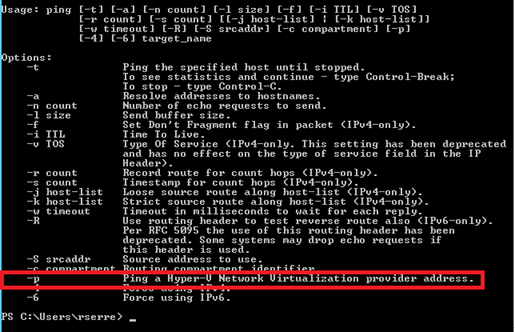
So I’m connecting to the first Hyper-V and I run the ping command:
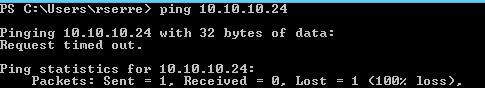
That’s doesn’t work. It is because you have to use –p with the ping:







Good writeup!