For this third day to TechEd Europe 2014, I went to these sessions:
- Session 1: Designing Hybrid scenario with Microsoft Azure;
- Session 2: Malware Hunting with Mark Russinovich and the Sysinternals Tools;
- Session 3: Microsoft Azure Security Compliance Overview;
- Session 4: Hyper-V Management made easy with System Center and Veeam Management Pack for System Center;
- Session 5: Planning and Designing Management Stamps with Azure Pack;
- Session 6: Managing Platform-as-a-Service with the Azure Pack.
So this is a big day with 6 sessions (no way to play games to win a Surface Pro 3 today in the Tech-Expo :p).
Session 1
The first presentation was about Hybrid Cloud with Microsoft Azure. The speaker began his presentation by the fact that the new model is the consumption of resources as CPU, RAM, storage and so on. This is why cloud computing is emerging. So there are two types of cloud:
- On-Premises Private Cloud;
- Off-Premises IaaS, SaaS, PaaS and so on called also Public Cloud.
To make Private Cloud with Microsoft technologies, you should use Windows Server, System Center and Windows Azure Pack. The implementation of Public Cloud is made across Microsoft Azure. This service provides a large panel of services as networking, automation, computer services and data services. To unify the Cloud Strategy, it is possible to use the best of the two worlds to make Hybrid Cloud.
The connection from On-Premises to Microsoft Azure can be implemented by using Site-To-Site VPN, Point-To-Site VPN or Express Route. Then the speaker has presented some hybrid cloud scenarios:
- Microsoft Azure Backup. Extending Windows Server Backup in the cloud (demo: Azure Site Recovery and Backup);
- Archive with StorSimple;
- Microsoft Azure Site Recovery;
- Presentation on SQL server with one server in On-Premises site and one in Microsoft Azure and he has created an AlwaysOn.
Next he presented the network with Microsoft Azure Virtual network. In this part the speaker introduced the security groups to manage network traffic rules between subnet. That enables to control access between virtual subnet.
To finish he talked about Azure Load-Balancer which works for IaaS and PaaS. This feature supports TCP and UDP, custom health probes and reserved IPs for Load-Balancing. A new feature is available that enables to make Source IP based affinity. It is also possible now to increase the idle connection timeout.
Session 2
The speaker was Mark Russinovich that presented how to hunt a malware. For that, he used SysInternals tools. He presented these malware cleaning steps:
- Disconnect from the network the infected machine;
- Identity Malicious processes and drivers;
- Check suspicious file as file with no icon, no description, unsigned Microsoft images, live in Windows Directory or user profile, strange url in the string, host suispicious dll or services, has an open tcp/ip endpoints and so on;
- Begin with task Manager then use SysInternals Process Explorer;
- Use Process Explorer to identify a strange process as a process that should not run in high privilege;
- Next process an image verification to see if a Microsoft signature is present;
- Presentation of VirusTotal.com that is an Antivirus-as-a-Service;
- Use of SysInternals SigCheck to check the signature of application.
- Terminate identified processes;
- Don’t kill the process because there are often a watchdog that restart it automatically;
- Instead of kill the process, suspend it.
- Identify and delete malware autostarts;
- Use SysInternals Autorun tools;
- Autorun is now able to connect to VirusTotal.com.
- Tracing Malware;
- Use SysInternals Process Monitor;
- Use filter to find more precisely what malware make.
- Malware Forensics;
- SysInternal Sysmon;
- Background system monitoring utility. First written for use in Microsoft corporate network.
- Delete the malware;
- Reboot and repeat.
At the end, the speaker has made presentation of malware hunting on Scareware and so on.
Session 3
This session is not really a technical session but it will give me information about how Microsoft assumes security on Microsoft Azure. When I talk with friends about Microsoft Azure it is difficult to find arguments for Microsoft Azure about security. This is why I have participated to this session.
The speaker first said that the cloud can be only adopted if the customers can be sure that security will be as good or better than on their On-Premises datacenters. First the speaker described how they identify and address threats before they impact customers with for example Digital Crime Unit. Next he talked about the shared responsibility between the customer and Microsoft:
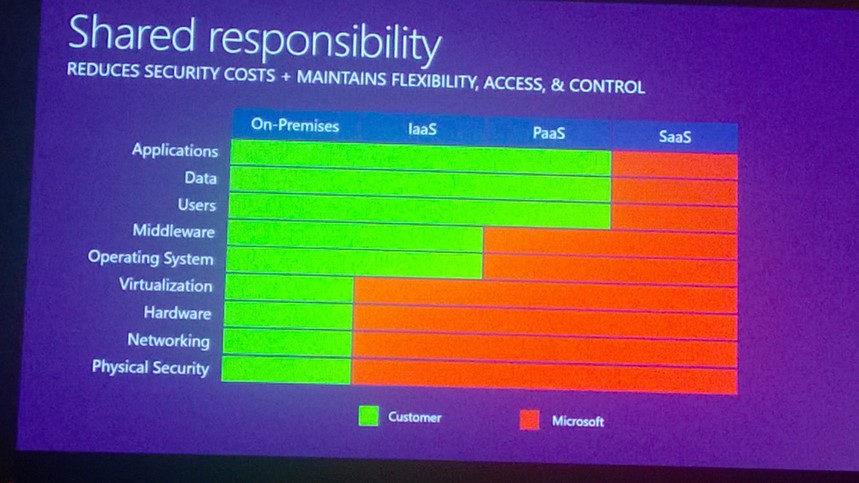
The next part of this session was more technical. First he talked about physical Datacenter security with for example camera, 24/7 security staff, barriers, alarms and so on. Then he talked about the patch management, monitoring & logging, antivirus & anti-malware and IDS to protect Microsoft Azure infrastructure and customer.
Next he introduced isolated virtual network with the new feature called Network Security Groups (cf. Session 1). He also presented the VPN and ExpressRoute between On-Premises site and Microsoft Azure in case of Hybrid Cloud.
Then he said a word about Identity & access management with Azure Active Directory to provide enterprise cloud identity and access management for end users, enable SSO and offers Multi-Factor authentication.
Microsoft Azure traffic is encrypted with SSL/TLS (HTTPS). Microsoft Azure supports FIPS 140-2, Bitlocker, EFS and Transparent Data Encryption for SQL. RMS service is also available to make file encryption. StorSimple is able to use AES-256 to encrypt data.
Next the speaker has presented this incident response presentation:

To finish with this session, the speaker said a word about “where is my data and who can access it?”. First customer can choose the region to store data:

The data stored in Microsoft Azure can be accessed by restricted Microsoft people. To limit access to customer data, Microsoft has implemented Just in time & Role-Based access. Microsoft does not provide any government access to data stored in Microsoft Azure. For EU customer data, there is a special contractual close. Moreover Microsoft Azure doesn’t share data with its advertiser supported services.
To finish when a data is deleted, index is immediately removed from primary location. Then a Geo-Replication of the index is run.
Session 4
In this session, Mike Resseler made a presentation of the Veeam Management Pack for SCOM. He presented the topology view that shows storage, network and virtual machine of a hypervisor (VMWare or Hyper-V). Thanks to this topology view, we can find easily which component cause an issue and which Virtual Machines is impacted.
Next he said a word about Veeam Task Manager for Hyper-V (free tool) to view the resource consumption of a Hyper-V host and its VMs in Real-Time.
Then he returned to SCOM and has introduced Veeam SCOM widget and the analysis Dashboard. This last enables to view easily the resource utilization (CPU, Memory, Memory Pressure etc.) by a VM or a hypervisor.
Next he presented the capacity planning which show analysis of resource consumption to plan hardware upgrade.
To finish he shown us a dashboard to find zombie VMs based on performance analysis. This report enables also to find oversized VMs.
Session 5
This presentation has been presented by Kristian Nese. First he presented the basics of VM Clouds. (SPF, VMM etc.) and the interaction between each component. Next he introduced the multi-tenancy in the Windows Azure Pack with hosting plans and subscription components. Several hosting plan can be associated to the same VMM.
The Service Provider Foundation can support 5 VMM stamps. If VMM and SPF are installed in a separate domain, the VMM domain must trust the SPF domain. Each stamp is an isolated stamp that means stamps can’t interact between them. To finish WAP supports only one SPF endpoint.
Below the use case for multiple stamp:

Below the use case for a single stamp for WAP:

When deploying VM Clouds for production, Virtual Machine Manager should be deployed in high availability. Hyper-V that host NVGRE gateway should be deployed in high availability and the Gateway Server also. Host-Groups should represent the location of Hyper-V hosts and then the function.
Bare-Metal Deployment should be used to deploy new Hyper-V host to be scalable. Moreover it is necessary to manage updates on hypervisors with WSUS integration for example. To finish you should have a high availability storage as Scale-Out File Server or SAN. It is better if storages support SMB 3.0 in order to manage it directly in VMM.
Next Kristian Nese presented a scenario with a single VMM stamp. In this case, VMM must scale across locations and NVGRE must be implemented (must also support tenants with VLANs). He also implemented Remote Console, and VM Role.
Next he has made a demo to implement the above described scenario.
You can find further information about Windows Azure Pack and VM Clouds on Tech-Coffee here.
Session 6
First the speaker talked about each server roles of WebSite Clouds:
- Controller – Provisions and manage other roles
- Management – REST endpoint to manage WAP WS
- Worker – Process web requests
- Front-End – Accepts web requests and routes to workers
- Publisher – Supports multiple publishing protocols
- File Server – Web Site shared storage (SOFS not supported)
- Database – SQL Server for System information
Next he presented the interaction between each server. You can find a schema here.
Then he switched on Windows Azure Pack admin portal to show a demo of Website cloud. The speaker explained features available as PHP, ASP.net, the management of level service etc.
Microsoft tested the stability of deployment 200+ web workers and 25,000 websites. Next he introduced the Web App Gallery that enables tenants to deploy easily WordPress, phpBB and so on.
Visual Studio can be used to deploy source code in a production Webfarm. Next he made a demo of the Websites tenant experience. He shown us how to create an empty website and how to deploy a website from the Gallery. To finish speaker explained how to use SQL database and MySQL database with websites.